Since this summer Defender Advanced Threat Protection supports also macOS. Now I had time to review the functionality and share my experience in this blog.
First of all, my starting position is a MacBook Air, which is enrolled to Microsoft Intune and is able to retrieve Configuration Profiles. The device is connected to the internet without a proxy server, therefore all the connection tests can be executed successfully.
Onboarding
 |
Navigate to the Security Center at https://securitycenter.windows.com and choose in the settings section the Onboarding link. |
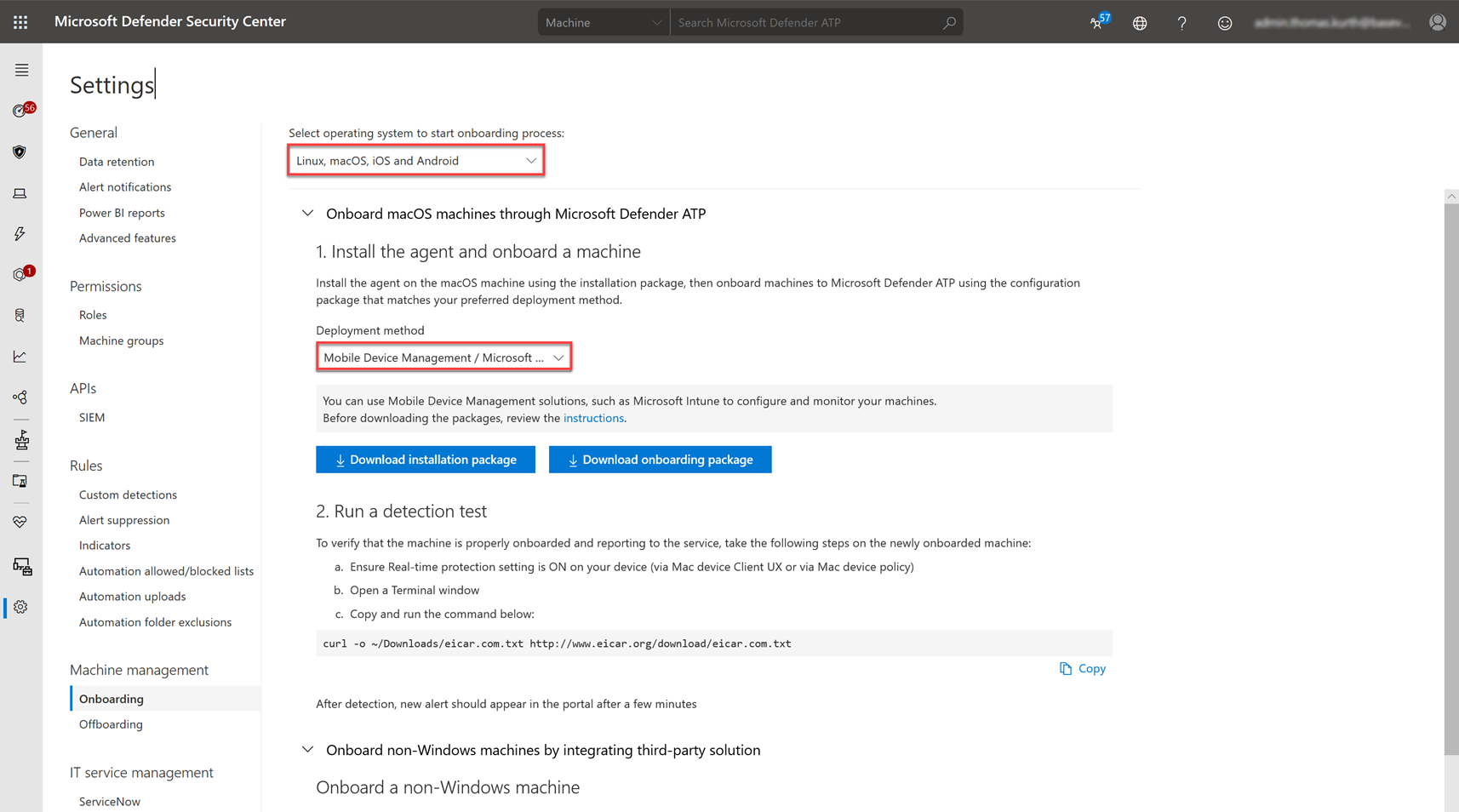 |
Choose «Linux, macOS, iOS and Android» from the OS selection dropdown. Then select in the next dropdown «Mobile Device Management». Then you are able to download the installation package and the onboarding package. |
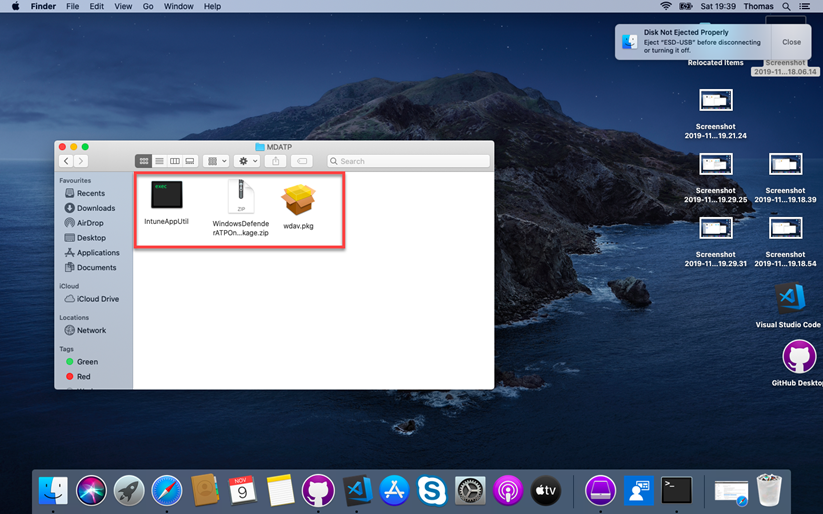 |
Now you have to download the IntuneAppUtil which is required to create an app which can be deployed with Intune. You can retrieve the binaries directly from the following url: https://docs.microsoft.com/intune/lob-apps-macos
If you have extracted all the files in the same folder, it should look like on the screenshot. |
 |
Now we are ready and you can start the Terminal to executed various commands.
As soon you have the terminal started, navigate to the folder where your files are. For windows users, you can use “cd” like in the cmd console ;). |
 |
First we have to mark the IntuneAppUtil as executable:
chmod +x IntuneAppUtil Then we can extract the zip file: unzip WindowsDefenderATPOnboardingPackage.zip Next, we can create the intunemac file with the following command: ./IntuneAppUtil -c wdav.pkg -o . -i "com.microsoft.wdav" -n "1.0.0" |
 |
After executing the commands in the last step, you got the new intunemac file in the same folder which we can then upload to Intune in the next step. |
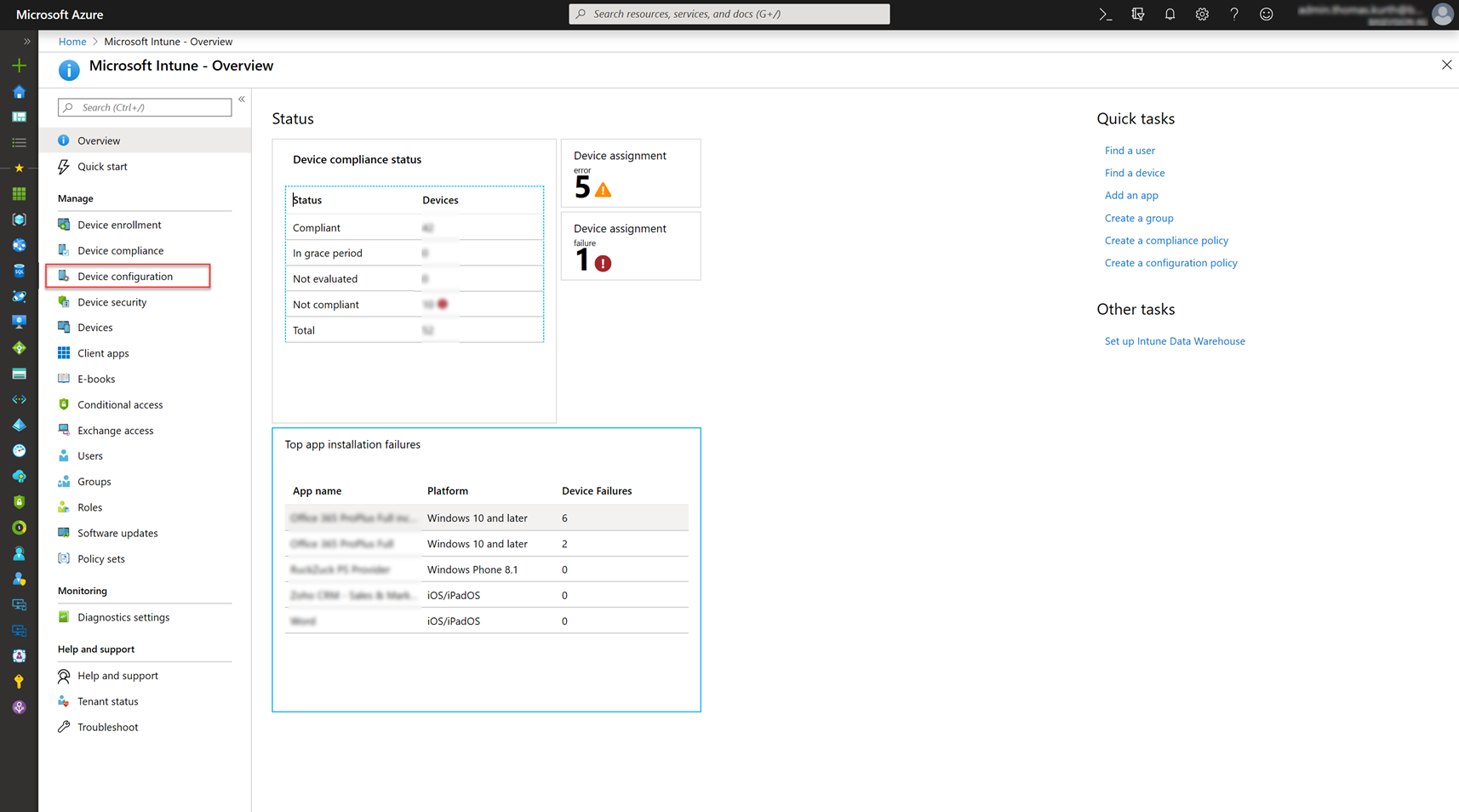 |
Open the Intune Portal and navigate to Device Configuration. |
 |
Then click on Profile… |
 |
… and then on Create Profile. |
 |
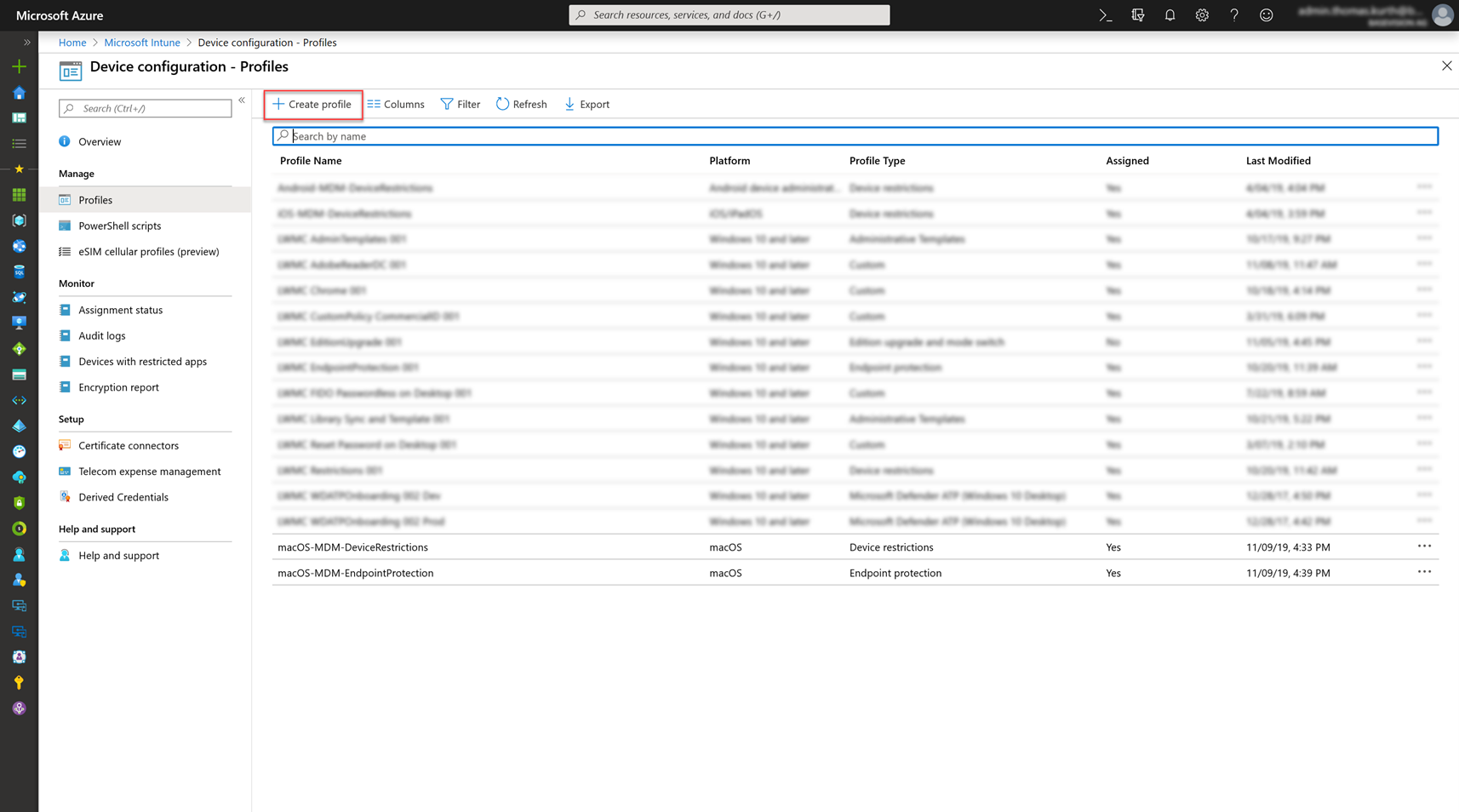
Give the profile a name and choose macOS and custom as the profile. Upload the kext.xml file which can be found in the Intune folder of the zip file.
Assign the profile to a group or to all devices. |
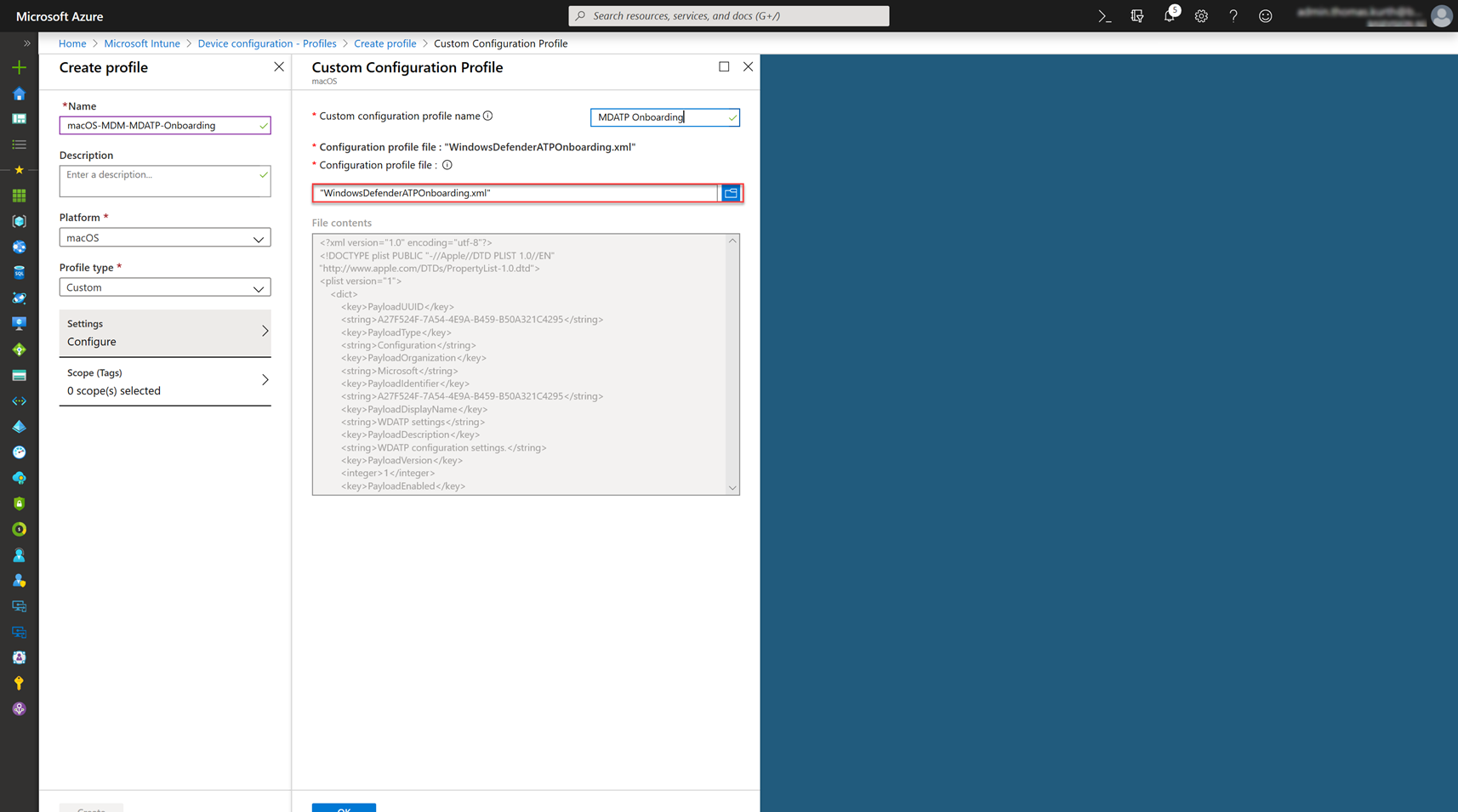 |
Create an additional Profile with the content of the WindowsDefenderATPOnboarding.xml file and assign it to the same group. |
 |
Then create an additional custom profile (tcc.xml) with the content which can be found in the following manual from Microsoft: |
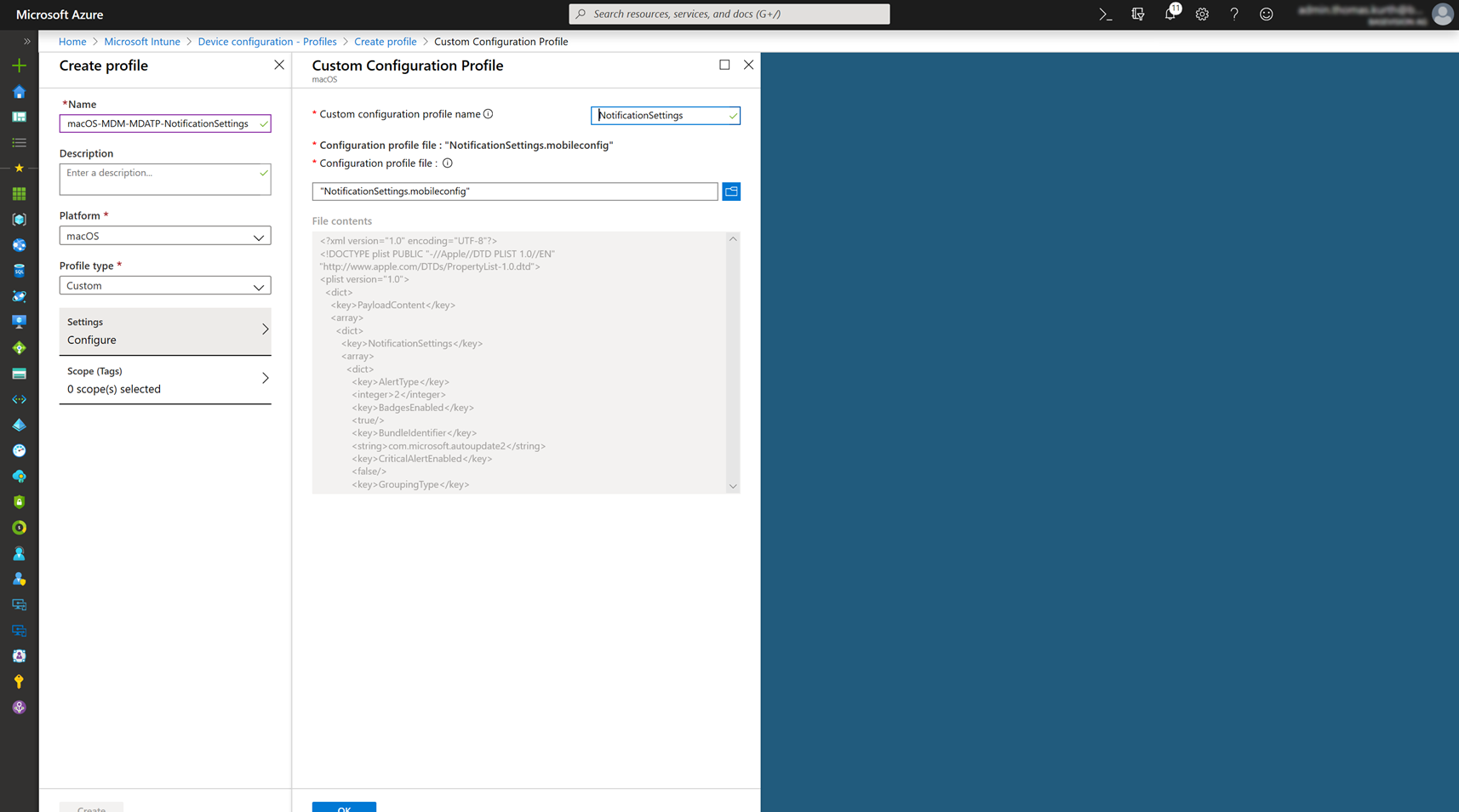 |
Lastly you must create another profile to configure the correct notification settings. You can download the correct file from Microsoft and create the .mobileconfig.
Again, assign the profile to your devices. |
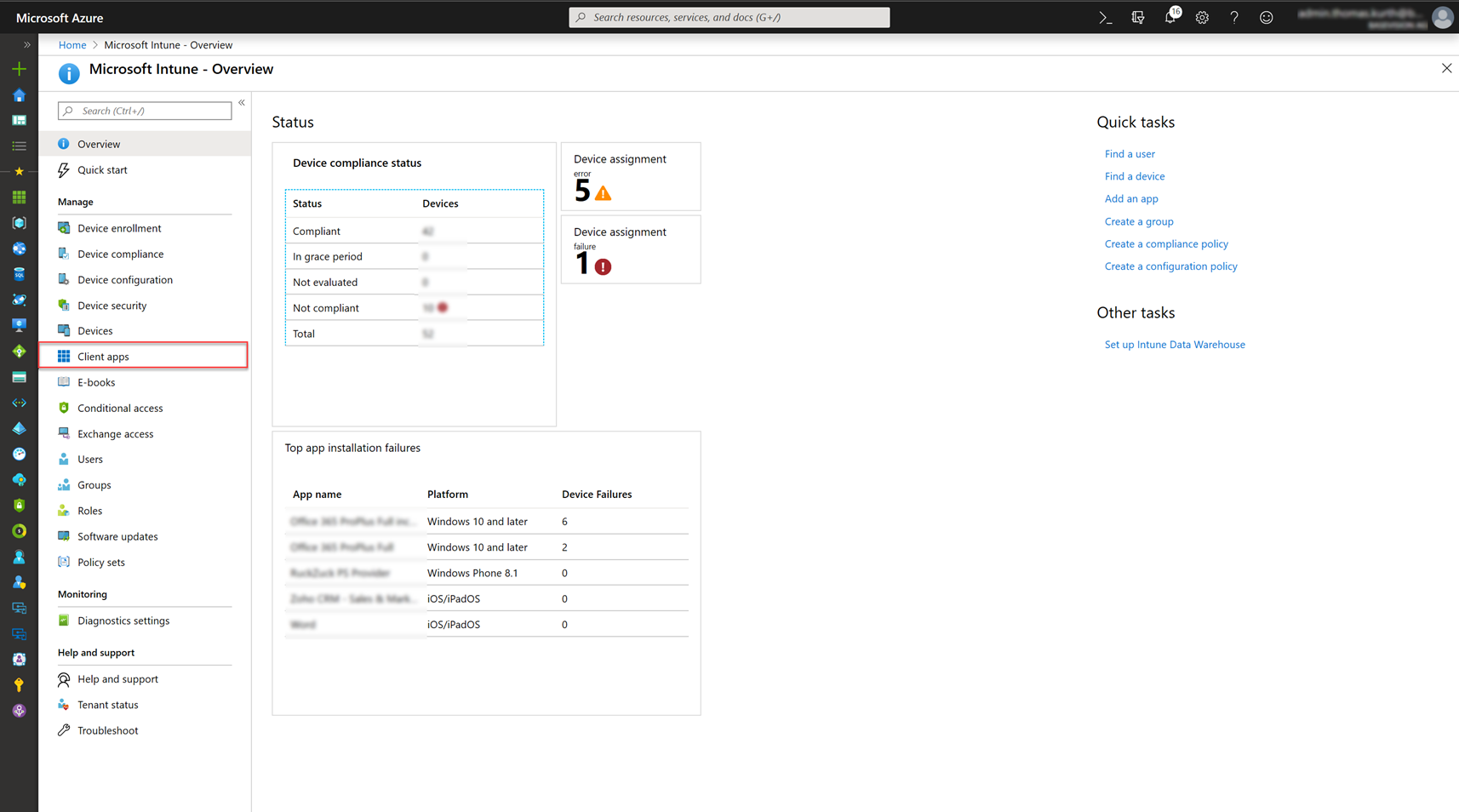 |
Go back to the main page of the Intune Portal and navigate to Client Apps. |
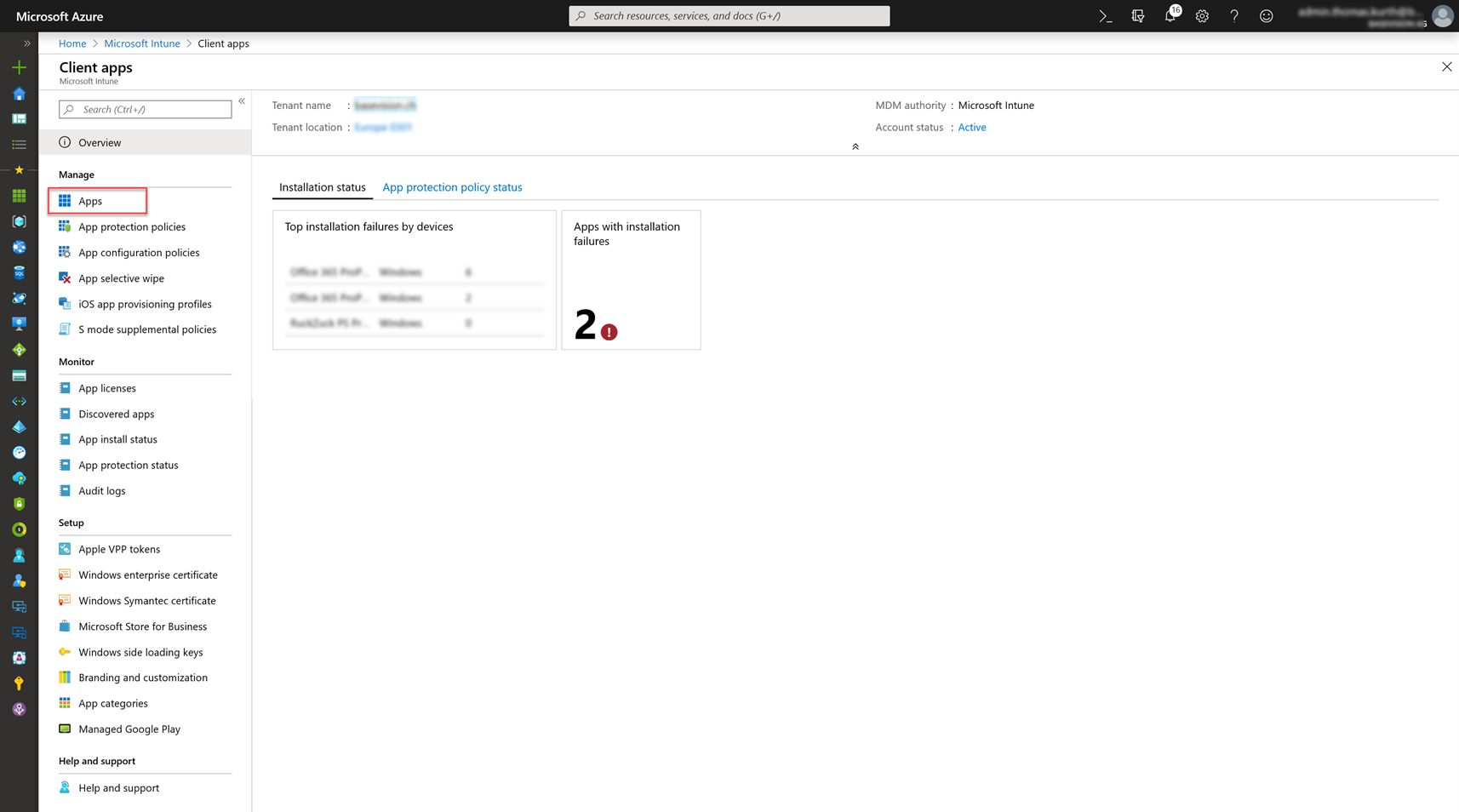 |
In the Client Apps section, we have to go to Apps. |
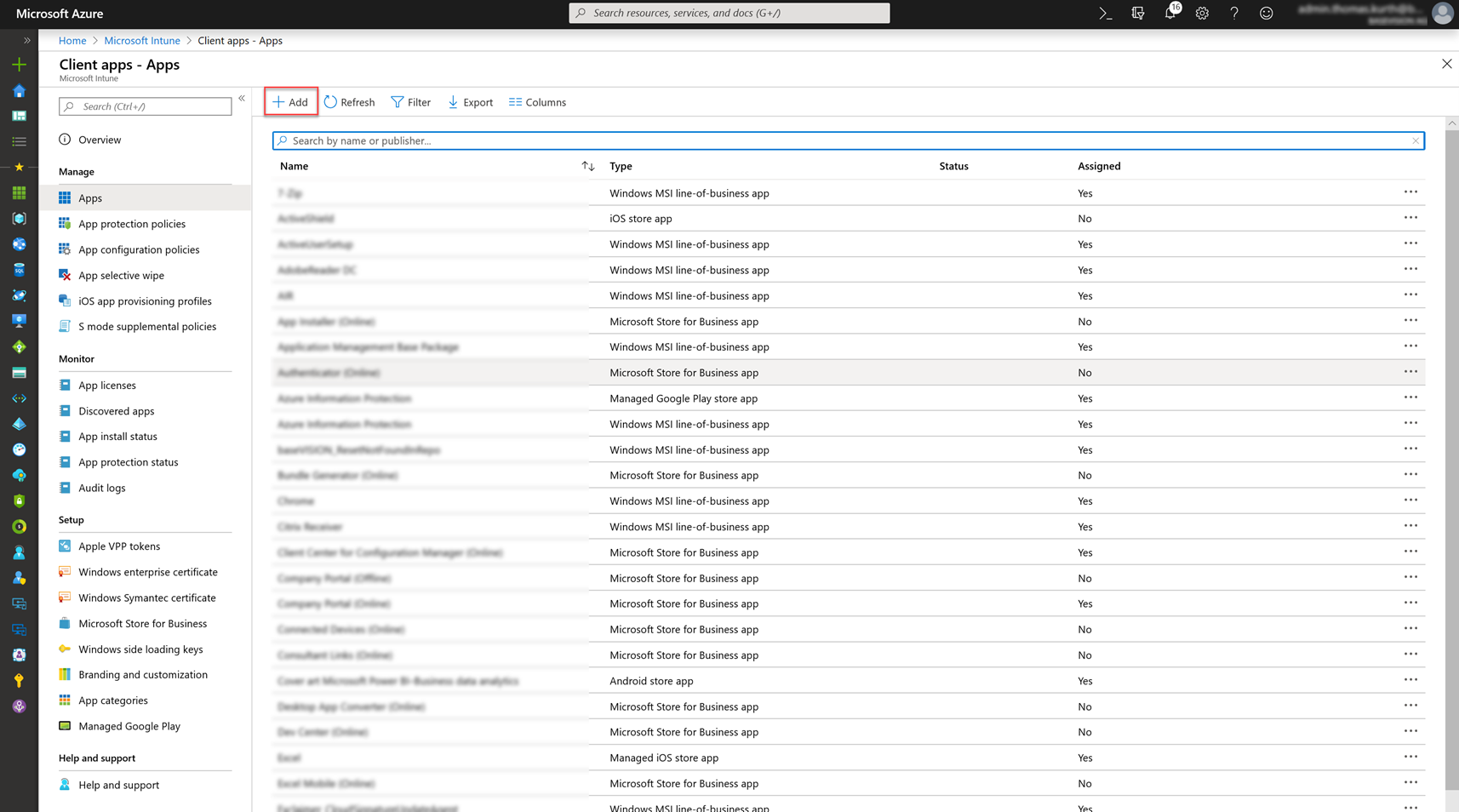 |
Now we see all our applications and can add a new one by clicking on Add in the top bar of the table. |
 |
Select «Line-of-business app» and then upload the generated intunemac file in the App package file. |
 |
Then specify the metadata in the App information blade. I chose as minimum operating system Catalina. |
 |
Now, you have to wait until the application is completely provisioned in Intune. As soon the application is ready to be assigned, assign it like the profiles. |
Result
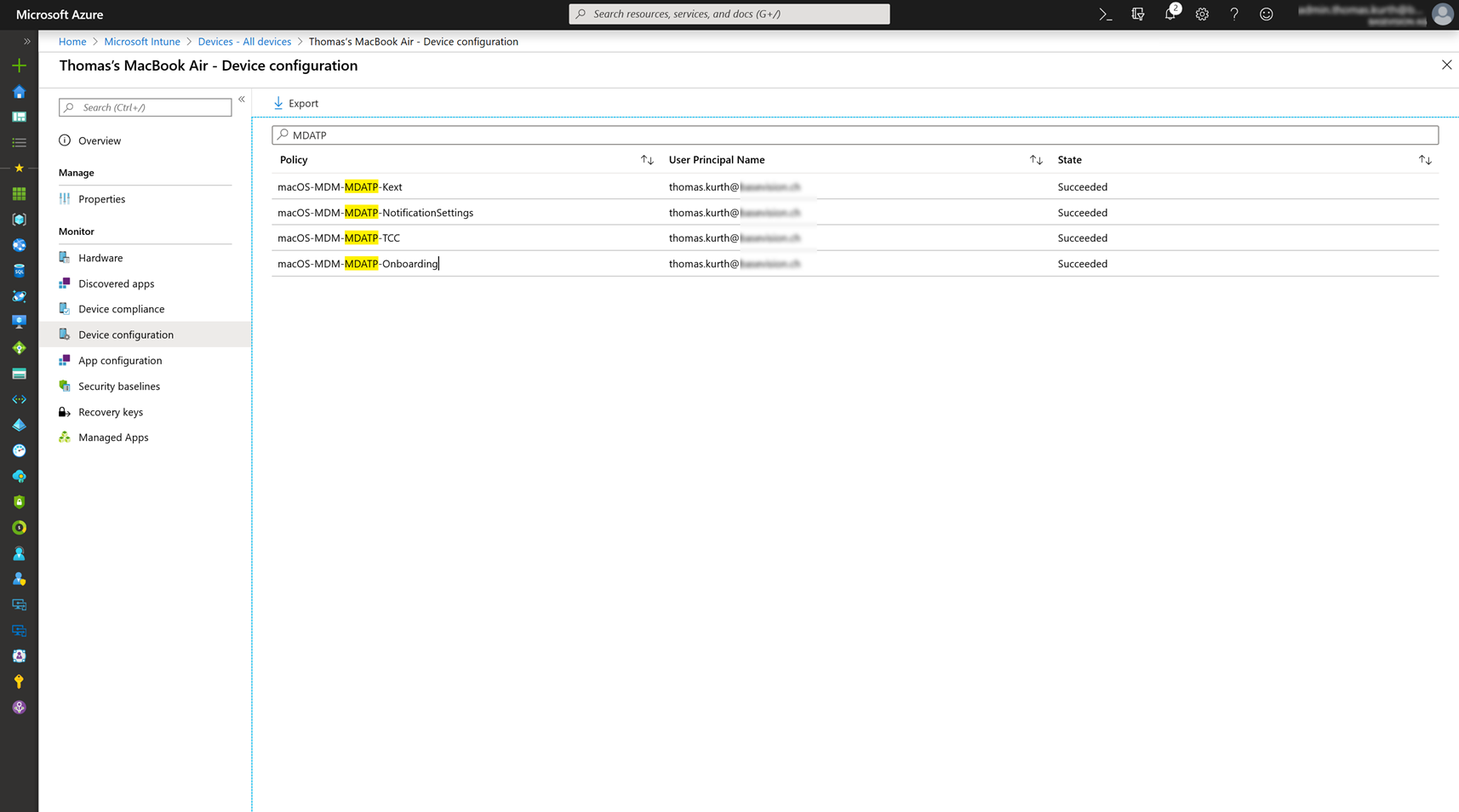
After a few minutes we can see, that all profiles are applied successfully to the devices and also the app was deployed successfully.
On the device the MDATP console is also displayed and I can see that the patterns are up-to-date and start a Quick Scan of my machine:
And even better, I can now see my MacBook Air also in the Defender Security Center which enables me to see all device events from all my devices in a single console. I was really surprised how fast an alert is displayed in the console. For example, as I downloaded the Eicar test file, I looked one second later to my other pc and saw already the alert in the console!
So, as you can see it’s easy to deploy this new capability and use MDATP to protect your Apple device like the Windows machines.
- Microsoft Sentinel ASIM Parser demystified - March 31, 2024
- Enhancing Network Security Insights with IDS/IPS of Ubiquiti Dream Machine Pro and Microsoft Sentinel - March 10, 2024
- Ubiquiti Dream Machine Pro Logs to Microsoft Sentinel - February 6, 2024






0 Comments