After the implementation of Conditional Access policies, it’s important to monitor the coverage status to check if all sign-ins are covered by a conditional access rule. But it’s important to know that it is highly likely that the coverage in a normal environment will never be 100%. This blog is dedicated to explain why some of the sing-in entries can be ignored during the analysis.
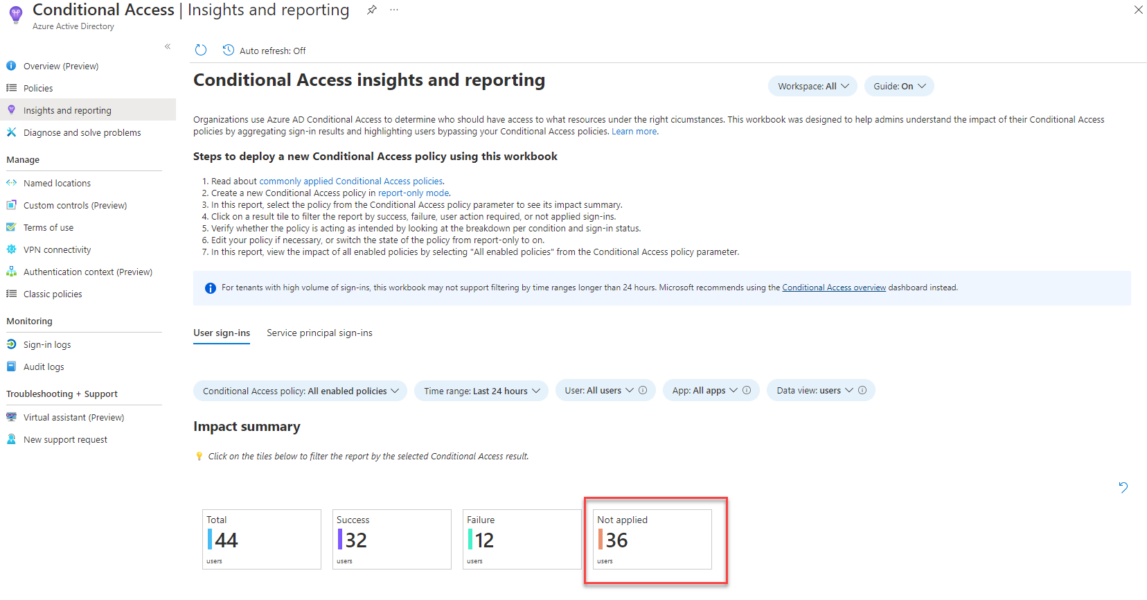
Especially the insights and reporting provided within the Conditional Access section will lead many customer towards the journey to more deeply analyze the Not applied status.
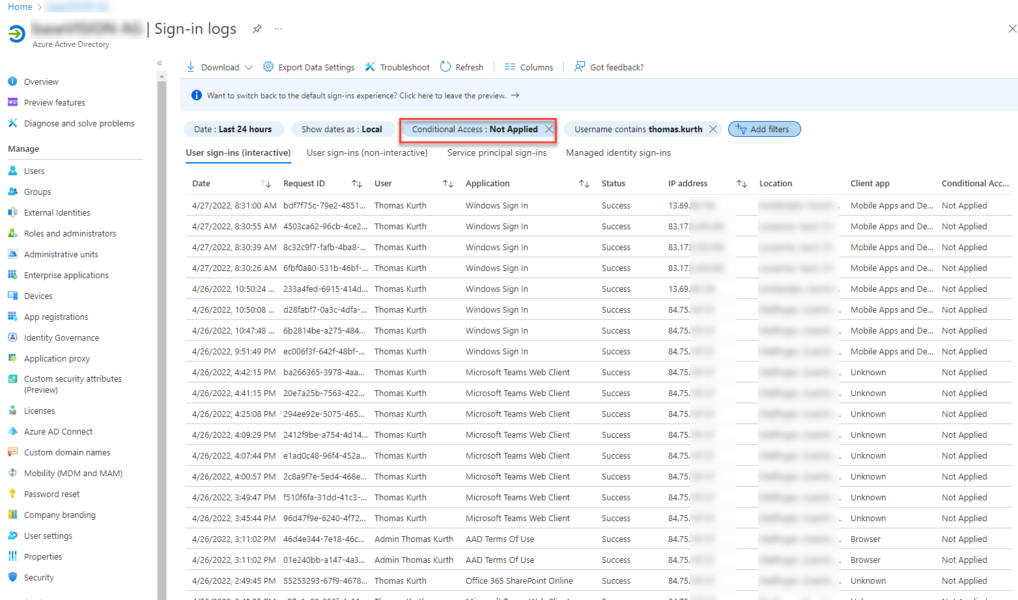
Windows Sign In
Some Applications like the “Windows Sign In” do not support Conditional Access. This Application is used when a user is logging on to a Azure AD Joined device, which can be Online and Offline. As the default Windows logon screen is not based on a Web-UI it is not possible to do Conditional Access checks.
B2B Sign In
When analyzing the Sign-In log and you detect “Microsoft Teams Web Client” or “Office 365 Sharepoint Online” in the list then it gets confusing. Why the hell is CA not applied. The answer is simple: It’s a B2B access.
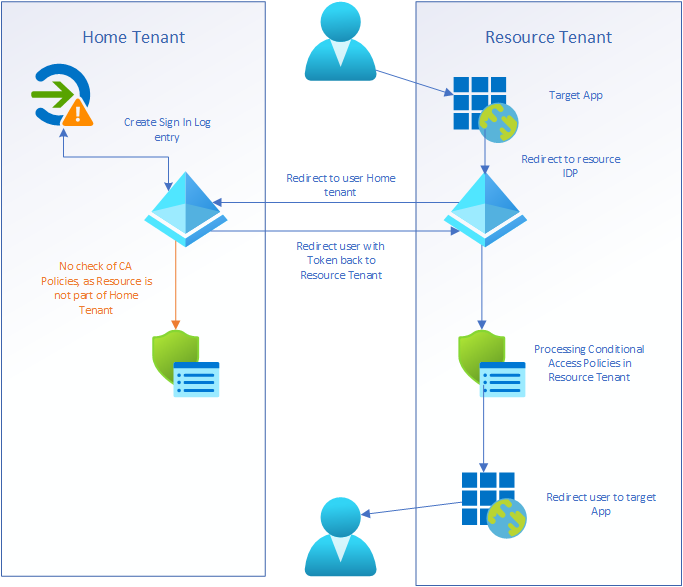
Microsoft highlighted the access flows in docs well but has not explained when a Sign In entry is created.
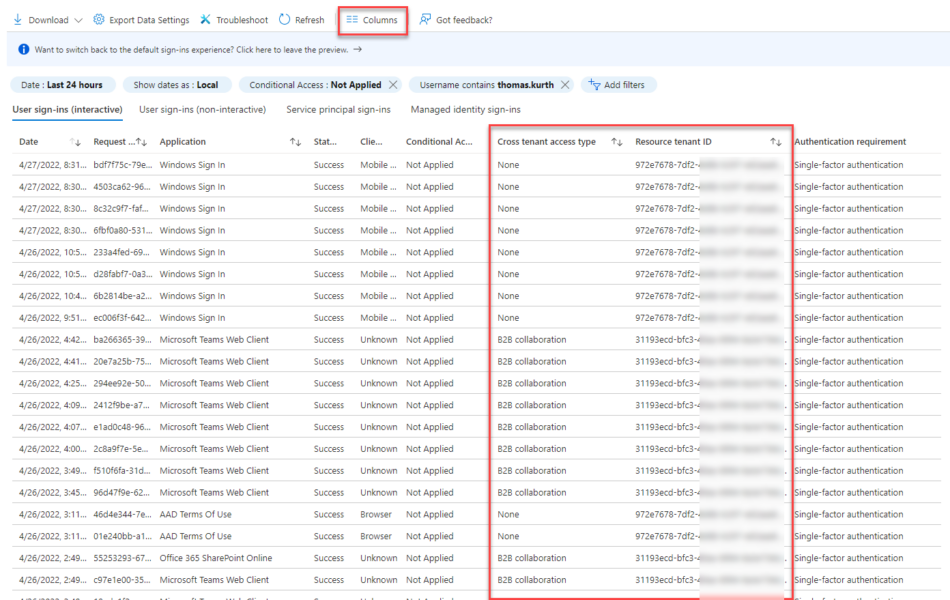
Through the new Cross Tenant Access settings the information in the sign in logs was expanded, which helps us to analyze the NotApplied status.
With the above information and by checking the redirections when accessing such a resource, then we can elaborate the following behavior flow:
Summary
With all the learnings I did during the investigation of this issues I can now better check if environments are really protected by Conditional Access or not. I hope that with this post a lot of readers will save time analyzing them in their infrastructure. Keep in mind the Conditional Access “NotApplied” sign ins are not in all cases a Conditional Access Policy misconfiguration!
- Microsoft Sentinel ASIM Parser demystified - March 31, 2024
- Enhancing Network Security Insights with IDS/IPS of Ubiquiti Dream Machine Pro and Microsoft Sentinel - March 10, 2024
- Ubiquiti Dream Machine Pro Logs to Microsoft Sentinel - February 6, 2024



0 Comments