Intune is the fast growing device management solution of Microsoft. One main functionality of Intune are compliance policies, which allow the verification of specific settings on a device. There is one missing feature, which I hope will be added soon, but for the time being I developed a workaround and share it with you. In compliance policies you can define actions for non-compliance, at the moment you have only two options:
- Mark the device as non-compliant (immediately or with a delay)
- Send an E-Mail to the end-user and optionally to fix defined users (immediately or with a delay)
The first option is good an helpful together with Azure AD Conditional Access, but the second one is not always optimal. For example, when your users do not have administrative permissions, then the e-mail can be confusing to the end-user. Also you can’t use dynamic strings, for example what setting is non-compliant and how it can be remediated. Additionally, a lot of companies would like to see such alerts in their Splunk/SIEM system or create an incidents in the ticketing system. The providers of such solutions have often a possibility to receive e-mails and to parse the information in it, but the mail messages of Intune are so generic, that no helpful events/incidents can be created.
Solution
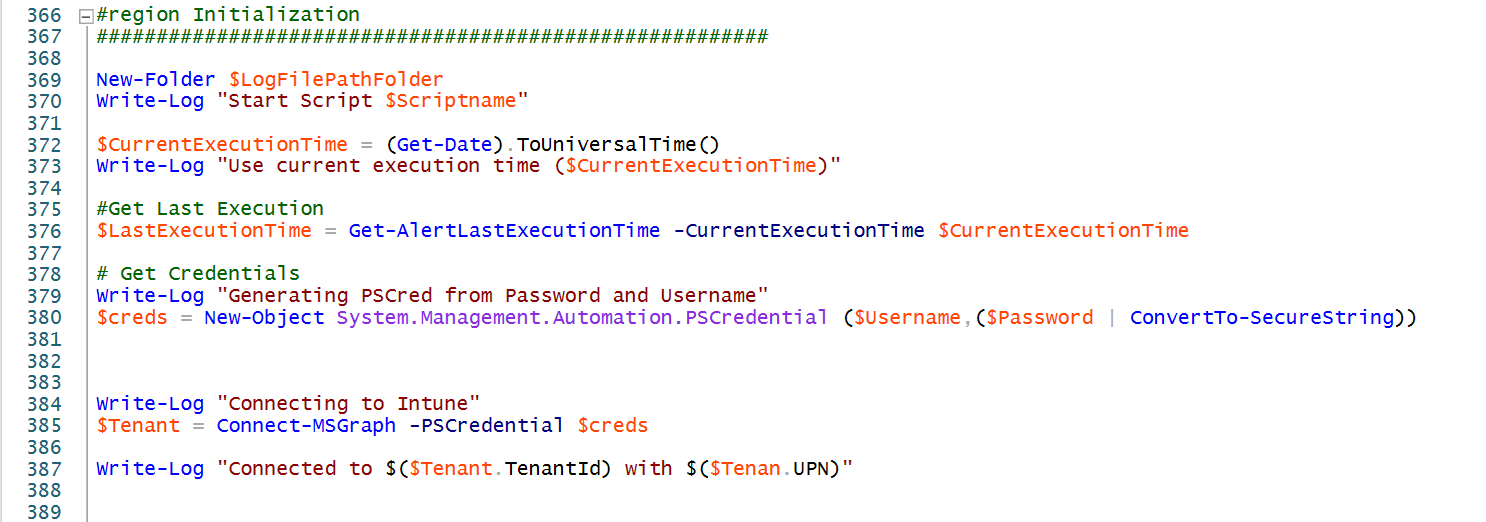
How do we get these alerts? Sure…. The Microsoft Graph API helps us and we are able to retrieve the events easily. I created a script which can be run as a scheduled task on a Windows box in your environment. I also preperad a version for Azure Automation, but there the Intune PowerShell module has some difficulties to load. Therefore, I suggest to only use the ScheduledTask.ps1 version from Github. The Script polls every time executed the devices which are marked as non-compliant since the last script executions. Therefore I recommend to execute it at least hourly to get the alerts as fast as possible.
Installation and configuration
If you have never used the Intune PowerShell Module, then install it on your device and grant Admin consent by executing the following commands:
Install-Module Microsoft.Graph.Intune Connect-MSGraph -AdminConsent
Then download the ScheduledTask.ps1 script and save it to your disk and open it with your preferred editor. You can see the configurations sections directly on the top of the script.
In the first configuration section you have to configure if you would like to monitor all devices or only MDM managed. Additionally, you have to provide credentials fort he user who should connect to MS Graph. This user requires at least read device permissions in the Intune tenant.
#region Intune Monitor Variable Definition
########################################################
# Only monitor these types of devices ("mdm","eas","easMdm")
$managementAgents = @("mdm")
## Username (MFA should not be enabled)
$Username = "admin@kurcontoso.onmicrosoft.com"
# As SecureString "Read-Host -AsSecureString | ConvertFrom-SecureString"
$Password = "01000000d08...…..8f26b1dafbaba8ff78"
#endregion
In the next section you can configure the remediation actions. The settings are directly documented in the code and should be self-explaining.
#region Remediation Actions Variable Definition
########################################################
# Only monitor these types of devices ("Mail","Splunk","Webhook")
$remediationActions = @("Webhook")
## Splunk
## Sends event to Splunk Rest API
$SplunkToken = "C3ABEA0B-1439-4070-AA51-7216E2DB3105"
$SplunkUrl = "http://SERVER:PORT/services/collector/event"
## Invoke Webrequest
## Sends complete Intune Device Object as JSON by submitting a HTTP POST request to the specified Url
$WebRequestUrl = "https://prod-111.westeurope.logic.azure.com:443/workflows/c5eb5c9b5e414d62bc905dd48e1ff910/triggers/manual/paths/invoke?api-version=2016-06-01&sp=%2Ftriggers%2Fmanual%2Frun&sv=1.0&sig=AZyxcxLYhmTywYy1Ez9Muejqxcyxc56ywk"
## Send Mail
$SmtpServer = "localhost"
$SmtpPort = 21
$SmtpFrom = "sender@mydomain.com"
$SmtpTo = @("support@mydomain.com")
$SmtpSSL = $true
$MailSubject = "New Intune Non-CompliantDevice"
#endregion
When you have finished the configuration then you can create a scheduled task. At the moment the script writes also settings to the registry and therefore requires admin privileges, but you can change that easily if you like by modifying the “$RegistryKey” variable. The first time started it will generate an alert for devices which where non-compliant since the last hour. Afterwards it will read the Last execution date from registry. So, if you are testing, you probably have to reset the time in registry to test your remediation actions.
Add your own remediation actions
You can create own remediation actions or modify my existing ones, but please share them back, so that others also can learn from you. In my mind are actions like automatically wipe a device when non-compliant for a specific time period and much more…
The remediation actions are triggered in the main script region:
ForEach($alert in $NewAlerts){
Write-Log "Processing Alert for $($alert.deviceName)"
if($remediationActions -contains "Webhook"){
Invoke-SendAlertWebhook -IntuneDevice $alert
}
if($remediationActions -contains "Splunk"){
Invoke-SendAlertToSplunk -IntuneDevice $alert
}
if($remediationActions -contains "Mail"){
Invoke-SendAlertMail -IntuneDevice $alert
}
}
Microsoft Flow as Webhook remediation action
The mail remediation actions is self explaining and the Splunk integration is only possible if you have Splunk in-place. Therefore I will demonstrate the functionality with Microsoft Flow.
 |
Navigate to https://flow.microsoft.com and create a new flow “Automated – from blank”. |
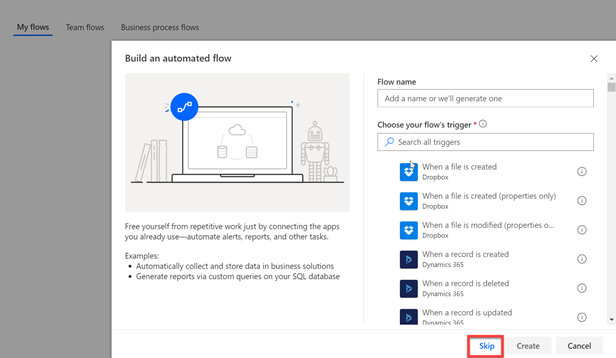 |
Just choose skip on this screen. |
 |
Now you can search for “request” and then you should see a trigger “When HTTP request is received”. Click on it. |
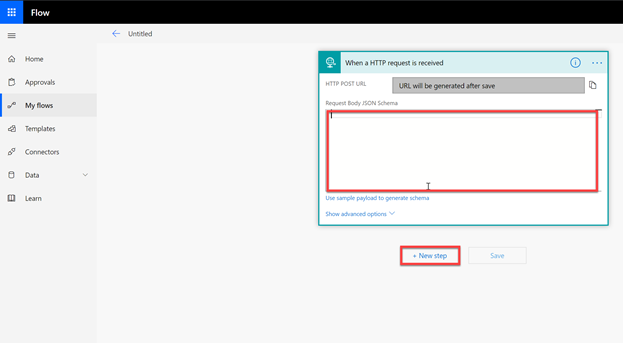 |
Now you can insert the JSON schema which is also available on Github.
{ After that click on “New Step” |
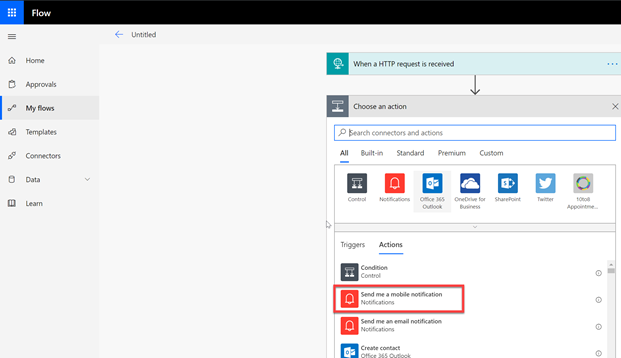 |
You can choose any action, but for testing I always rely on the “Send me a mobile notification” action. Select it. |
 |
If you click into the “Text” textbox you can see, that you have full access to all variables the script sends to the webhook.
Then click on save. |
 |
Now you have to verify that you have a device which is non-compliant and that the LastExecutionTime entry is older than the time when the device got non-compliant.
Then execute the ScheduledTask.ps1 in powershell and wait a few seconds… |
 |
… and you should get the mobile notification. |
Conclusion
I hope this workaround to trigger remediation actions helps you until Microsoft adds more possibilities to the product itself. Stay tuned for an updated version as soon the Intune PowerShell module can be used in Azure Automation.
- Microsoft Sentinel ASIM Parser demystified - March 31, 2024
- Enhancing Network Security Insights with IDS/IPS of Ubiquiti Dream Machine Pro and Microsoft Sentinel - March 10, 2024
- Ubiquiti Dream Machine Pro Logs to Microsoft Sentinel - February 6, 2024




0 Comments